How PKI Works (Without Math): A Cybersecurity Perspective
The internet was never designed to be secure. Anyone can intercept traffic, impersonate services, or tamper with data. Yet every day, we confidently log into banks, send sensitive emails, and deploy software updates across the globe.
Public Key Infrastructure (PKI) is the invisible system that makes this possible.
This article explains how PKI works, why it matters to cybersecurity, where it can fail, and how attackers target it, without math or cryptography jargon.
The Core Problem PKI Solves
On the internet, you face two fundamental risks:
- Impersonation: Anyone can pretend to be anyone else
- Eavesdropping: Anyone on the network can read or modify data
If you connect to a website, how do you know:
- It is really the site you intended?
- No attacker is silently intercepting the connection?
PKI exists to solve trust and identity on untrusted networks.
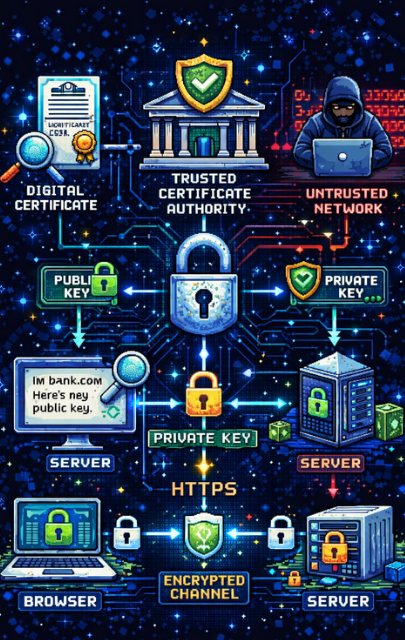
What Is PKI (In Simple Terms)?
PKI is a system that allows computers to prove identity and communicate securely using digital certificates.
It enables:
- Authentication (Who are you?)
- Confidentiality (Can anyone read this?)
- Integrity (Was this data altered?)
- Non-repudiation (Can the sender deny sending it?)
The Key Components of PKI
1. Public and Private Keys
Think of this as a lock and key system:
Public Key
- Shared openly
- Used to encrypt data or verify signatures
Private Key
- Kept secret
- Used to decrypt data or create signatures
If the private key is compromised, the identity is compromised.
2. Digital Certificates (Your Online ID)
A certificate is a digital identity card that says:
“This public key belongs to this organization or domain.”
It contains:
- The public key
- Owner identity (for example, a domain name)
- Expiration date
- Who issued it
- A digital signature from a trusted authority
Certificates prevent attackers from simply saying, “Trust me.”
3. Certificate Authorities (CAs): The Root of Trust
A Certificate Authority (CA) is a trusted organization that verifies identities and signs certificates.
Your operating system and browser already trust dozens of CAs by default.
When a CA signs a certificate, it is essentially saying:
“We have verified this identity. You can trust it.”
How PKI Works in the Real World (HTTPS Example)
Scenario: Visiting a Secure Website
When you visit https://example.com:
Step 1: The Server Sends Its Certificate
The server provides its certificate containing:
- Its public key
- Proof of CA verification
Step 2: Your Browser Verifies Trust
Your browser checks:
- Is the CA trusted?
- Is the certificate valid and not expired?
- Does the domain name match?
- Has the certificate been revoked?
If any check fails, you see a security warning.
Step 3: A Secure Channel Is Established
Using the public key, your browser establishes an encrypted session. Only the server’s private key can complete the process.
From this point on:
- Traffic is encrypted
- Attackers cannot read or modify data
- Identity is verified
Why PKI Is Critical to Cybersecurity
1. Stops Man-in-the-Middle Attacks
Without PKI, attackers could:
- Intercept traffic
- Pretend to be the server
- Steal credentials silently
PKI makes impersonation extremely difficult.
2. Enables Trust at Internet Scale
PKI powers:
- HTTPS
- VPN authentication
- Secure email (S/MIME)
- Code signing
- Device and IoT authentication
- Zero Trust architectures
Without PKI, modern cybersecurity would collapse.
3. Ensures Software Integrity
Code signing ensures:
- Software updates come from legitimate vendors
- Malware cannot masquerade as trusted software
This is essential for operating systems, cloud services, and enterprise deployments.
PKI Attack Vectors (How Attackers Target Trust)
PKI is cryptographically strong, but attackers rarely break the math. They attack keys, trust relationships, and human processes instead.
1. Private Key Compromise
This is the most common and most dangerous attack. Attackers steal private keys through:
- Malware on servers or endpoints
- Weak file permissions
- Insecure backups
- Keys hard-coded in source code
- Cloud storage misconfigurations
Impact:
- Full impersonation of the victim
- Decryption of intercepted traffic
- Signing of malicious code or certificates
From a defender’s view, private keys must be treated as crown jewels.
2. Man-in-the-Middle via Rogue Certificates
If attackers obtain a valid certificate for a domain they do not own, they can silently intercept traffic. This can happen through:
- Compromised Certificate Authorities
- Exploiting weak domain validation
- DNS or email hijacking during certificate issuance
Impact:
- Undetectable traffic interception
- Credential theft
- Session hijacking
Certificate transparency and monitoring help detect this class of attack.
3. Certificate Authority Compromise
This is rare but catastrophic. If a CA is breached:
- Attackers can issue trusted certificates
- Browsers and systems will accept them as legitimate
- Global trust can be broken instantly
Impact:
- Large-scale impersonation
- Nation-state level surveillance
- Emergency revocation across the internet
This is why CA trust is tightly controlled and audited.
4. Certificate Misconfiguration and Expiration Abuse
Attackers often exploit operational failures rather than cryptography. Common issues:
- Expired certificates causing outages
- Weak cryptographic algorithms still enabled
- Incorrect domain bindings
- Reuse of keys across multiple systems
Impact:
- Denial of service
- Forced downgrade attacks
- Security bypasses during outages
Many high-profile outages are PKI failures, not attacks.
5. Weak or Deprecated Cryptography
Older systems may still accept:
- Weak signature algorithms
- Short key lengths
- Legacy TLS configurations
Attackers exploit this by forcing weaker connections.
Impact:
- Easier traffic decryption
- Reduced trust guarantees
- Compliance failures
Modern systems must enforce strong cryptographic policies.
6. Trust Store Manipulation
Attackers who gain local or administrative access may:
- Install malicious root certificates
- Modify trust stores
- Bypass certificate validation entirely
Impact:
- Silent interception of encrypted traffic
- Full visibility into supposedly secure communications
This is commonly seen in malware, enterprise spyware, and advanced persistent threats.
PKI in Modern Security Architectures
Today, PKI is central to:
- Zero Trust networking
- Mutual TLS authentication
- Cloud workload identity
- Secure DevOps pipelines
- Device and service authentication
Identity, not network location, is now the security boundary.
Real World PKI Failure Story: The DigiNotar Breach
In 2011, the global trust model of the internet quietly broke.
DigiNotar was a small but trusted Certificate Authority based in the Netherlands. Like other CAs, its root certificates were embedded in major operating systems and web browsers. This meant that any certificate DigiNotar issued would be automatically trusted by millions of systems worldwide.
Attackers managed to breach DigiNotar’s internal network. Once inside, they gained access to the systems responsible for issuing digital certificates. This was the worst place an attacker could be in a PKI environment.
Over a period of time, the attackers issued more than five hundred fraudulent certificates. These were not obviously fake. They were properly formed, correctly signed, and trusted by browsers. Among the certificates issued were ones for high value domains such as Google, Yahoo, Microsoft, and Mozilla.
One of the most impactful certificates was for Google.com.
With a valid Google certificate in hand, attackers were able to perform man in the middle attacks against users. When victims attempted to access Google services over HTTPS, their browsers showed the familiar lock icon. There were no warnings. Everything appeared secure.
In reality, encrypted traffic was being intercepted, decrypted, and monitored.
Investigations later revealed that users in Iran were specifically targeted. The fraudulent certificates allowed attackers to spy on email, search queries, and account activity while users believed they were protected by HTTPS.
The cryptography did not fail.
The browsers did not fail.
The users did nothing wrong.
The failure occurred because the trust model assumed that all trusted Certificate Authorities would always remain secure.
Once the breach was discovered, the response was drastic. Browser vendors removed DigiNotar from their trusted root stores. Overnight, every certificate issued by DigiNotar became untrusted. The company collapsed shortly afterward.
This incident permanently changed how PKI is managed. It led to the adoption of:
- Certificate transparency logs
- Stricter CA audits
- Improved revocation mechanisms
- Greater monitoring of certificate issuance
The DigiNotar breach demonstrated a hard truth about PKI. Trust on the internet is only as strong as the weakest trusted authority. When a single CA fails, the impact can be global.
Final Thoughts
PKI is not just cryptography. It is the foundation of digital trust.
Attackers do not break PKI by solving math problems. They break it by stealing keys, abusing trust, and exploiting misconfigurations.
When PKI is properly implemented and managed, attacks fail silently. When it is ignored or misunderstood, breaches become inevitable.
Understanding PKI and its attack surface is essential for anyone working in cybersecurity.
