Browser-in-Browser (BiB) Attacks: When the Browser UI Becomes the Phishing Vector
Introduction
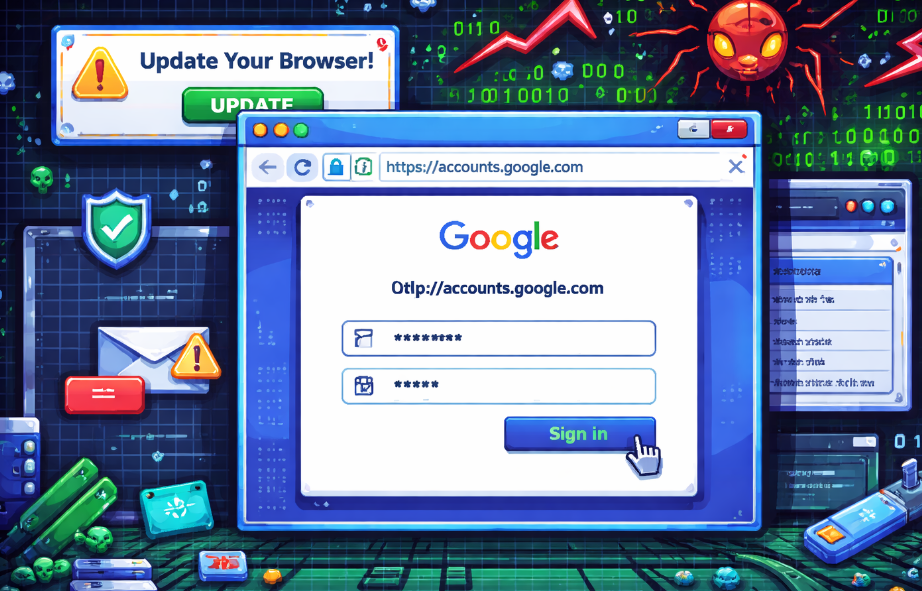
Browser-in-Browser (BiB) attacks represent a modern evolution in phishing techniques. Rather than relying on fake domains or malicious browser popups, this approach abuses standard web technologies to replicate trusted browser interface elements inside a web page itself.
What makes BiB attacks particularly effective is that they do not exploit software vulnerabilities. Instead, they exploit user trust in familiar browser UI elements such as address bars, lock icons, and well-known login providers challenging long-standing assumptions about how users verify authenticity online.
What Is a Browser-in-Browser Attack?
A Browser-in-Browser attack is a phishing technique in which a website renders a fake browser window within the page using HTML, CSS, and JavaScript. The fake window is designed to look like a real browser popup and often imitates OAuth login dialogs from major identity providers.
From the user’s perspective, the window appears legitimate:
- It looks like a separate browser window
- It displays a familiar URL and HTTPS indicator
- It follows expected login workflows
In reality:
- The “window” is part of the page’s DOM
- The displayed URL and lock icon are only visual elements
- Any credentials entered are sent to the attacker
No browser exploit or malware is required.
Why This Technique Is Effective
1. Trust in Browser Chrome
Users are routinely trained to verify:
- HTTPS
- Domain names
- Familiar login providers
BiB attacks directly imitate these trust signals, rendering visual verification unreliable.
2. Legitimate Web Capabilities
Modern browsers intentionally support advanced UI rendering, including:
- Custom window styling
- Absolute positioning
- Drag and resize behavior
These features are necessary for rich web applications but also enable convincing UI deception.
3. OAuth Normalization
OAuth login flows commonly appear as popups. Users are conditioned to accept these prompts quickly, reducing scrutiny when a fake window appears.
Browser-in-Browser Attacks on Compromised Legitimate Websites
Browser-in-Browser attacks are not limited to clearly malicious or newly registered domains. A particularly dangerous scenario occurs when legitimate, trusted websites are compromised and used as the delivery platform.
In these cases, attackers inject malicious JavaScript into an existing site that users already trust. Common compromise vectors include:
- Vulnerable CMS plugins or themes
- Stored or reflected cross-site scripting (XSS)
- Compromised third-party JavaScript (analytics, chat widgets, ad networks)
- Supply-chain attacks against shared libraries or CDNs
Once embedded, the attacker can deploy a Browser-in-Browser interface directly within the trusted site. From the victim’s perspective:
- The domain in the real browser address bar is correct
- HTTPS is present
- The login prompt appears contextually appropriate
This significantly increases the success rate of the attack, as users associate phishing with suspicious or unfamiliar websites not with sites they already trust.
From a defensive standpoint, this highlights an important reality:
- HTTPS alone does not guarantee safety
- Domain reputation is an insufficient trust signal
- Website compromise can turn legitimate platforms into phishing infrastructure
Related UI-Deception Technique: Fake Browser Update Pop-Outs
A closely related and long-standing technique involves fake browser update pop-out windows, often presented as urgent security or compatibility updates (e.g., “Your browser is out of date” or “Critical security update required”).
While often discussed separately, this technique relies on the same core principle as Browser-in-Browser attacks: abusing user trust in browser-level UI and messaging.
In these attacks:
- A webpage displays a modal or pop-out styled to resemble a browser or system update dialog
- Branding and language mimic legitimate vendors (Chrome, Firefox, Edge)
- The prompt urges immediate action to continue viewing content or to remain secure
Modern versions of these attacks increasingly:
- Simulate native browser update dialogs with high visual accuracy
- Use draggable, window-like interfaces similar to BiB popups
- Deliver malware, remote access tools, or additional phishing stages
When hosted on compromised legitimate websites, fake update pop-outs are especially effective because:
- The site itself is trusted
- The update request appears contextually plausible
- Users are conditioned to accept frequent browser updates
Although fake update pop-outs may not always involve credential harvesting, they share the same UI deception model as Browser-in-Browser attacks and are often used in combination with them during multi-stage compromise campaigns.
Relationship to Other Attack Techniques
Browser-in-Browser attacks function primarily as a delivery mechanism and are often combined with other techniques, including:
- Credential phishing
- Adversary-in-the-Middle (AiTM) attacks
- Session hijacking
- MFA token interception
- Malware delivery via fake updates
In advanced campaigns, credentials and MFA responses may be relayed to the legitimate service in real time, allowing attackers to capture authenticated session cookies rather than passwords.
Adoption by Advanced Threat Actors
Although initially observed in commodity phishing campaigns, Browser-in-Browser techniques have increasingly appeared in operations attributed to more sophisticated threat actors, including espionage-focused groups.
For such actors, BiB offers several advantages:
- No malware deployment required (at least initially)
- Minimal forensic footprint
- High success rate against trained users
- Effective even on fully patched systems
When combined with fake browser update pop-outs, attackers can transition seamlessly from credential access to endpoint compromise.
Why Traditional Security Controls Often Miss BiB
Browser-in-Browser attacks commonly bypass:
- Antivirus and EDR tools (no executable payload at first)
- Network intrusion detection (legitimate HTTPS traffic)
- URL reputation systems (often hosted on trusted domains)
- TLS inspection (content appears benign)
Effective detection typically requires:
- Behavioral analysis
- DOM inspection
- Context-aware authentication monitoring
- Identification of anomalous OAuth and update-prompt behaviors
Defensive Considerations
For End Users
- Password managers are a strong defense, as they bind credentials to real domains
- Browser updates should only be performed through official browser menus or vendor sites
- Unexpected login or update prompts should raise suspicion
- Reloading the page or opening a new tab may expose fake UI elements
For Organizations
- Prefer full-page OAuth redirects over popup-based logins
- Enforce strict Content Security Policies (CSP)
- Audit and monitor third-party scripts
- Treat website compromise as both a phishing and malware delivery risk
For Security Teams
- Classify BiB and fake update pop-outs as UI-deception techniques
- Include both scenarios in phishing simulations
- Monitor authentication anomalies and suspicious download initiation events
Key Takeaway
Browser-in-Browser attacks and related techniques such as fake browser update pop-outs underscore a critical shift in the threat landscape:
Modern phishing increasingly targets human trust in browser interfaces rather than technical flaws.
Because these attacks can be delivered through both malicious domains and compromised legitimate websites, defenses must extend beyond visual cues and traditional perimeter controls.
Understanding how attackers abuse browser-like UI is now essential for effective user education, secure web design, and incident response.
